Secure Your Identity: Advanced Facial Recognition Verification Techniques


Advanced Facial Recognition Verification technology has revolutionized security measures, offering a seamless and efficient way to verify identity. From airports to financial institutions, organizations are utilizing this technology to enhance security, improve user experience, and reduce costs.
However, there are drawbacks to consider, such as biases and privacy concerns. Understanding the different types of facial recognition, including 2D, 3D, and thermal imaging, is crucial for effective implementation.
Despite its benefits, addressing challenges such as technical limitations and ethical issues is necessary for successful integration.
What Is Facial Recognition Identity Verification?
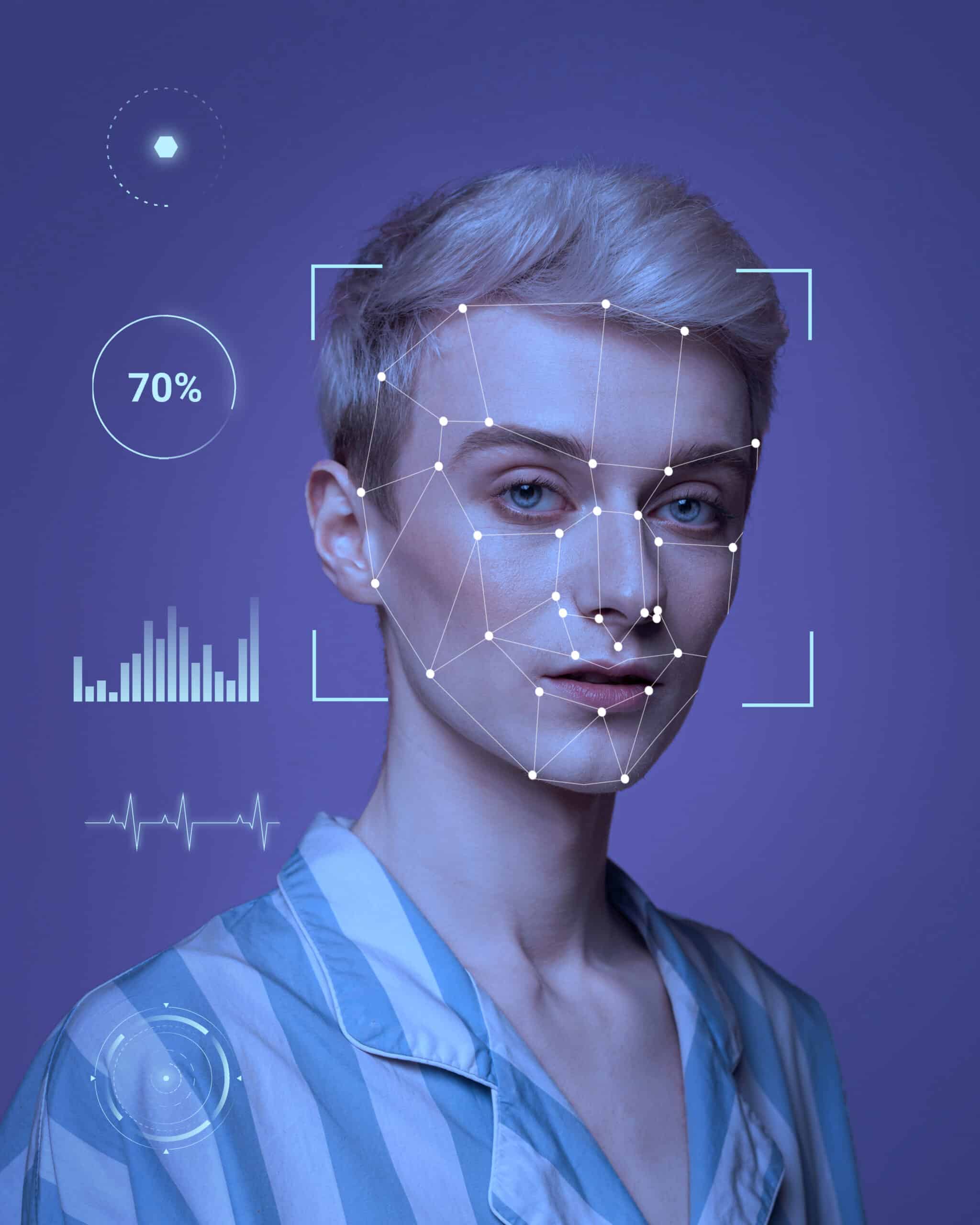
Facial Recognition Identity Verification is a cutting-edge technology that utilizes biometric authentication techniques to verify the identity of individuals by analyzing their facial features.
This process involves capturing and storing key points of an individual’s face, such as the distance between their eyes, the shape of their nose, and the contours of their lips. Also, the system compares these unique facial characteristics to a database of known identities to confirm or deny access. The use of artificial intelligence algorithms helps in accurately matching these facial features, making the verification process efficient and secure.
By relying on the distinctiveness of each person’s face, facial recognition identity verification provides a sophisticated layer of security in applications ranging from smartphone unlocking to airport border control.
How Does Facial Recognition Identity Verification Work?
Facial Recognition Identity Verification operates by deploying advanced technology, such as machine learning and artificial intelligence, to accurately authenticate user identity through facial biometrics.
These innovative technologies work by analyzing unique facial features, such as the distance between eyes or the shape of the jawline, to create a biometric template specific to each individual. Machine learning algorithms continuously improve accuracy by learning from a vast dataset of facial images, refining their ability to distinguish between different faces. Additionally, artificial intelligence plays a crucial role in swiftly processing these biometric patterns, enabling rapid identification and verification of users. Together, these technologies revolutionize security measures by offering a seamless and efficient solution for identity authentication.
What Are The Benefits Of Facial Recognition Identity Verification?
Facial Recognition Identity Verification offers enhanced security measures by leveraging advanced technology to secure access and enhance authentication processes within security systems.
This technology provides a high level of accuracy in identifying individuals through their facial features, reducing the risk of unauthorized access. By integrating facial recognition, organizations can strengthen access control by ensuring that only authorized personnel are granted entry. This system can be seamlessly integrated with existing security infrastructure, making it a cost-effective solution for enhancing security measures.
The use of facial recognition technology eliminates the need for physical access cards or passwords, reducing the chances of security breaches. Additionally, facial Recognition Identity Verification presents a robust and efficient way to enhance security protocols and ensure secure authentication processes.
Enhanced Security
Enhanced Security is a core benefit of Facial Recognition Identity Verification, providing robust measures for access control, ensuring a secure environment, and implementing stringent security protocols.
Utilizing facial recognition technology offers unparalleled security enhancements by incorporating biometric authentication, which adds an extra layer of protection against unauthorized access. The system ensures only authorized individuals can enter restricted areas, minimizing the risk of breaches. By adhering to rigorous security protocols, such as encryption of captured data and continuous monitoring, organizations can maintain a high level of security and data integrity. This comprehensive approach to security not only safeguards sensitive information but also enhances overall operational efficiency.
Improved User Experience
Improved User Experience is a key advantage of Facial Recognition Identity Verification, offering seamless and secure access, streamlined identity management, and enhanced security for transactions.
Facial Recognition technology has revolutionized the way users interact with systems by providing a convenient and reliable authentication method. Through the use of biometric data, individuals can access their accounts and information with just a glance, eliminating the need to remember complex passwords or carry physical tokens. This not only saves time but also enhances the overall user experience.
Facial Recognition Identity Verification ensures that only authorized users can perform secure transactions, minimizing the risk of fraudulent activities and enhancing trust in the system.
Cost-Effective
Cost-Effective solutions are provided by Facial Recognition Identity Verification, offering efficient security solutions that aid in fraud prevention and overall cost reduction.
This innovative technology not only enhances security measures but also streamlines processes, leading to significant savings for organizations by reducing manual labor costs.
By accurately identifying individuals, Facial Recognition Identity Verification eliminates the need for costly password resets, ID badge replacements, and traditional security protocols.
The system’s real-time verification capabilities result in quicker authentication processes, enhancing overall operational efficiency.
With its ability to quickly detect and deter fraudulent activities, it serves as a proactive defense mechanism, minimizing financial losses associated with fraudulent transactions.
What Are The Drawbacks Of Facial Recognition Identity Verification?
Despite its advantages, Facial Recognition Identity Verification faces challenges such as biases and inaccuracies, privacy concerns, and limited accessibility in certain scenarios.
For instance, one of the major issues with facial recognition technology is its tendency to exhibit racial biases, wherein certain ethnic groups are more likely to be misidentified compared to others. This not only raises concerns about fairness and equity but also highlights the potential social implications of using such technology.
The collection and storage of vast amounts of biometric data for facial recognition systems raise serious privacy issues, as this data can be vulnerable to breaches or misuse if not adequately protected. The reliance on facial features as the primary mode of verification may pose challenges for individuals with certain disabilities or those from diverse backgrounds whose facial characteristics may not align with the algorithms used for identification.
Biases And Inaccuracies
Biases and inaccuracies in Facial Recognition Identity Verification can arise from detection algorithms and face detection processes, leading to potential errors in authentication.
Detection algorithms play a critical role in identifying unique facial features for authentication; however, they may exhibit biases towards certain demographics, such as race or gender, resulting in misidentification. Face detection techniques, including landmark detection and feature extraction, also face challenges in accurately capturing facial nuances, potentially leading to false positives or negatives. These inaccuracies can have far-reaching implications, particularly in security and privacy-sensitive applications, where an erroneous authentication could grant unauthorized access or deny legitimate users.
Privacy Concerns
Privacy concerns associated with Facial Recognition Identity Verification revolve around data privacy, the risk of identity theft, and the need for robust privacy protection measures.
One of the major challenges with Facial Recognition Identity Verification is the potential misuse of personal data. As facial recognition technology becomes more widespread, there is a growing fear that sensitive information could be accessed and exploited by unauthorized parties. This poses a significant threat to individuals’ privacy and raises questions about who has access to this data and how it is being used.
Implementing effective privacy protection mechanisms is crucial to address these risks and safeguard the rights of individuals undergoing identity verification.
Limited Accessibility
Limited accessibility is a drawback of Facial Recognition Identity Verification, impacting scenarios where monitoring and access management may be challenging or restricted.
In situations where individuals’ facial features are not easily captured due to poor lighting conditions or obscured views, the accuracy of facial recognition systems can be compromised, leading to authentication failures.
Certain environments pose challenges in maintaining a consistent database of authorized faces for comparison, potentially hindering the system’s effectiveness.
Issues related to privacy concerns and data protection also contribute to the limited accessibility of facial recognition technology, as stringent regulations may limit its deployment in certain industries or regions.
What Are The Different Types Of Facial Recognition Identity Verification?
Facial Recognition Identity Verification encompasses various types, including 2D recognition, 3D recognition, and thermal imaging techniques, each offering distinct approaches to identity authentication.
2D recognition involves analyzing two-dimensional images of a person’s face, commonly used in smartphones for unlocking devices. On the other hand, 3D recognition creates a depth map of the face, enabling higher accuracy in identifying individuals by capturing facial contours. Thermal imaging, a cutting-edge technology, measures heat patterns emitted by the face, useful in low-light conditions or for increased security measures. These different methods cater to diverse needs in authentication, from user-friendly applications to advanced security protocols.
2D Facial Recognition
2D Facial Recognition is a technique that relies on image processing for identity recognition, analyzing facial features within two-dimensional spaces for authentication purposes.
This technology captures facial features from images or video frames, using algorithms to locate key points like eyes, nose, and mouth. By comparing these distinct features against a database of stored templates, the system can identify individuals in various applications such as access control, surveillance, or personal device security.
The accuracy of 2D facial recognition systems depends on factors like lighting conditions, angle of the face, and image quality, making continuous advancements in this area crucial for improving its effectiveness and reliability.
3D Facial Recognition
3D Facial Recognition offers enhanced identity verification through three-dimensional analysis, ensuring secure communication channels and precise authentication measures.
This technology’s three-dimensional analysis capabilities allow for a more comprehensive and accurate representation of facial features, making it harder for unauthorized access. In secure communication applications, 3D Facial Recognition adds an extra layer of protection, as it requires a physical presence for authentication, reducing the chances of identity fraud. The accuracy it brings to identity verification processes streamlines security protocols and enhances overall user experience by eliminating the need for passwords or PINs, making it a convenient and reliable solution in various industries.
Thermal Imaging Facial Recognition
Thermal Imaging Facial Recognition utilizes heat signatures for detection and identity verification, enabling secure network access and efficient authentication processes.
This cutting-edge technology is revolutionizing security protocols by accurately capturing and analyzing unique heat patterns emitted by individuals. By incorporating thermal imaging into the facial recognition process, it enhances the accuracy and reliability of identifying individuals, even in low-light or challenging environmental conditions. This innovative approach to authentication provides a more secure and seamless user experience, making it ideal for a wide range of applications, from access control to border security.
How Can Facial Recognition Identity Verification Be Used?
Facial Recognition Identity Verification finds applications in diverse sectors such as airport security, border control, financial institutions, and law enforcement agencies for secure and efficient identity authentication.
- In airport security, facial recognition technology is utilized to enhance the screening process by quickly matching passengers’ faces against known databases, helping authorities identify potential threats or unauthorized individuals.
- Border control agencies have also integrated facial recognition systems to verify the identity of travelers, ensuring secure and seamless passage across borders.
- Financial institutions leverage this technology to strengthen customer authentication methods, reducing the risk of fraud and enhancing account security.
- Law enforcement agencies use facial recognition for identifying suspects, locating missing persons, and improving overall public safety measures.
Airport Security
Facial Recognition Identity Verification enhances airport security through efficient detection mechanisms and the use of secure platforms for identity authentication of passengers and personnel.
This technological advancement not only assists in identifying individuals accurately but also plays a crucial role in ensuring that only authorized personnel have access to restricted areas within the airport premises.
By seamlessly integrating with existing security systems, Facial Recognition Identity Verification can provide real-time alerts in case of any discrepancies, thereby enabling security personnel to take immediate action to prevent potential threats.
The ability to verify identities swiftly and accurately contributes significantly to the overall safety and security of airports, ultimately enhancing the travel experience for all passengers.
Border Control
Facial Recognition Identity Verification aids in border control activities by facilitating access management procedures and streamlining the identity verification process for border security measures.
This technology plays a crucial role in verifying the identity of individuals crossing international borders, ensuring the safety and security of the country. By integrating facial recognition into border control systems, authorities can swiftly authenticate travelers’ identities, detect fraudulent attempts, and monitor high-risk individuals in real-time. The use of facial recognition helps in reducing human error and expedites the overall screening process, allowing for efficient and accurate identification of individuals passing through border checkpoints.
Financial Institutions
Financial Institutions utilize Facial Recognition Identity Verification for secure transactions, ensuring compliance with security protocols and enhancing the overall safety of financial operations.
This cutting-edge technology enables financial organizations to verify the identity of individuals by analyzing unique facial features. By capturing and comparing facial biometrics, institutions can accurately confirm the identity of customers in real-time, reducing the risk of fraudulent activities. This process adds an additional layer of security to transactions, safeguarding sensitive financial information and preventing unauthorized access. Compliance with strict security standards is crucial in the financial sector, and Facial Recognition Identity Verification helps institutions meet these requirements efficiently and effectively.
Law Enforcement
Law Enforcement agencies deploy Facial Recognition Identity Verification for monitoring activities, detection algorithms, and identity validation processes to enhance security measures and investigative capabilities.
This advanced technology allows law enforcement officials to quickly identify individuals in real-time by analyzing facial features and comparing them to large databases of known faces. By using Facial Recognition Identity Verification, authorities can accurately track suspects, locate missing persons, and prevent potential threats more efficiently.
The system works by capturing live images or video feeds from surveillance cameras and applying sophisticated algorithms to recognize faces, thus providing a valuable tool for maintaining public safety and conducting thorough investigations.
What Are The Challenges In Implementing Facial Recognition Identity Verification?
The implementation of Facial Recognition Identity Verification encounters challenges like technical limitations, legal and ethical considerations, and issues related to public acceptance of this technology.
- One of the primary technical constraints faced in deploying facial recognition for identity verification is the accuracy and reliability of the system. Factors such as variations in lighting, facial expressions, and backgrounds can affect the performance of facial recognition algorithms.
- Concerns around data privacy and security pose legal and ethical dilemmas that must be addressed before wider adoption can occur. Gaining public trust and acceptance is crucial for the successful integration of this technology into various applications such as security systems or mobile devices.
Technical Limitations
Technical Limitations pose hurdles in Facial Recognition Identity Verification, necessitating the development of secure software, robust detection algorithms, and efficient monitoring mechanisms.
Ensuring the security and reliability of facial recognition technology is crucial in overcoming these challenges. Building secure software involves implementing encryption protocols, access controls, and regular security updates to prevent unauthorized access to sensitive data.
The effectiveness of detection algorithms plays a vital role in accurately identifying individuals, requiring continuous refinement and enhancement to handle diverse scenarios. Continuous monitoring processes are essential to detect and address any anomalies or inaccuracies in the verification process, enhancing the overall reliability and trustworthiness of facial recognition systems.
Legal And Ethical Issues
Legal and Ethical Issues surround Facial Recognition Identity Verification, encompassing concerns related to identity protection, potential security attacks, and the ethical implications of widespread surveillance.
Facial recognition technology has been praised for its convenience in various fields, from unlocking smartphones to enhancing security measures at airports. The deployment of this technology also raises complex legal and ethical dilemmas.
One major concern is the protection of individuals’ identities and personal data from potential misuse or unauthorized access. The reliance on facial recognition for identity verification poses security vulnerabilities, as hackers could potentially exploit loopholes in the system. This brings to light the ongoing debate about the balance between security measures and individual privacy rights in the context of surveillance practices.
Public Acceptance
Public Acceptance is a crucial challenge for Facial Recognition Identity Verification, requiring transparency in digital identity management and the adoption of effective identity verification techniques to gain trust.
Without building trust among users, the advancement and wide implementation of facial recognition technology in identity verification processes could face significant resistance.
Transparency in how personal data is collected, stored, and used is key to alleviating privacy concerns. By incorporating reliable identity verification methods that prioritize accuracy and security, organizations can demonstrate their commitment to protecting user data and fostering a secure digital environment.
Emphasizing the importance of user consent and data protection practices will help bridge the gap between technology advancements and public acceptance.
Frequently Asked Questions
What is facial recognition identity verification and how does it enhance security measures?
Facial recognition identity verification is a biometric technology that uses a person’s facial features to confirm their identity. It enhances security measures by providing an additional layer of authentication that is difficult to fake or duplicate.
How does facial recognition technology work?
Facial recognition technology uses an algorithm to analyze and map a person’s facial features, such as the distance between their eyes and the shape of their jawline. The system then compares this information to a database of known faces to confirm a person’s identity.
What are the benefits of using facial recognition for identity verification?
Facial recognition offers several benefits for identity verification, including increased accuracy, speed, and convenience. It also eliminates the need for physical IDs or passwords, reducing the risk of identity theft and fraud.
Is facial recognition technology secure?
Continuous improvements are being made in facial recognition technology, making it one of the most secure biometric authentication methods available. However, like any security measure, it is not infallible and can be vulnerable to hacking attempts or false positives.
How is facial recognition being used for security measures?
Facial recognition is being used for various security measures, such as airport security, law enforcement, and access control for buildings and devices. It is also being incorporated into mobile devices for secure unlocking and payment verification.
Are there any privacy concerns with facial recognition technology?
Privacy concerns surrounding facial recognition technology have raised, as it involves collecting and storing biometric data. However, stakeholders are taking measures to address these concerns, such as obtaining consent and securely storing data.